Introduction to Netzilo
Overview of Dashboard Components
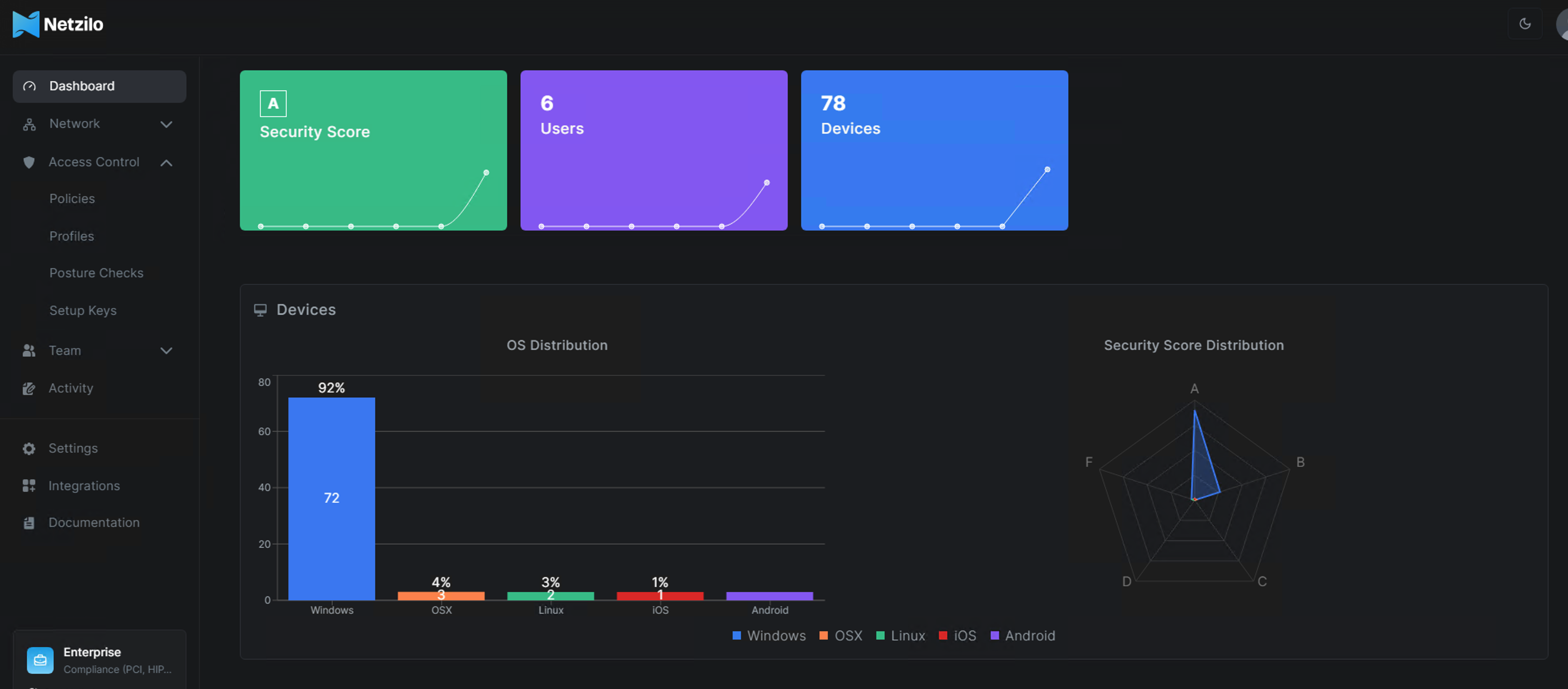
This section will explain the various components displayed in the security monitoring dashboard, as shown in the image. This dashboard is designed to provide a clear and comprehensive overview of your network's security posture, user activity, and device distribution.
1. Security Score
The Security Score component is a dynamic indicator that reflects the overall security posture of the devices within the monitored environment. This score is calculated based on several factors, including device configurations, security settings, software versions, and detected vulnerabilities. The score ranges from A (excellent) to F (poor), with A representing a robust security posture and F indicating significant risks. The visual representation of this score helps administrators quickly assess the security status and prioritize actions to mitigate risks.
2. Users
The Users component displays the total number of users currently being monitored within the network. This value is essential for tracking the scope of monitoring and understanding how many individuals are contributing to the overall security posture. The graph accompanying the user count shows the trend over time, allowing for easy observation of changes in user activity and potential impacts on security.
3. Devices
The Devices component indicates the total number of devices being monitored. This figure includes all devices connected to the network, such as desktops, laptops, mobile devices, and others. The accompanying graph provides a time-based view of how the number of devices has changed, which can be crucial for identifying spikes in device connections that may require further investigation.
4. Devices - OS Distribution
The OS Distribution section provides a detailed breakdown of the operating systems in use across all monitored devices. This bar chart highlights the percentage and absolute number of devices running on different operating systems, such as Windows, OSX, Linux, iOS, and Android. Understanding the OS distribution is critical for tailoring security policies and ensuring that all systems, regardless of platform, are adequately protected.
5. Security Score Distribution
The Security Score Distribution radar chart offers a granular view of the security posture across different categories (A through F). This chart helps visualize the spread of security scores among devices, making it easier to identify which devices fall into lower security categories and require immediate attention. The goal is to maximize the number of devices in the higher categories (A and B) while minimizing those in lower categories (D, E, F).
Netzilo is a platform that can be self-hosted. See a comparison between the self-hosted and cloud-hosted versions here.
There is no centralized VPN server with Netzilo - your computers, devices, machines, and servers connect to each other directly over a fast encrypted tunnel. It creates a high-performance point-to-point WireGuard® overlay network that connects machines running anywhere in just a few clicks.
It literally takes less than 5 minutes to deploy a secure point-to-point VPN with Netzilo.
How-To Guides
Route traffic to private networks
Learn how to provide access to LANs, VPS, and corporate private networks.
Configure default routes and traffic for the Internet
Understand how to set up your network for accessing the internet through default routes, also known as "exit nodes".
Log and monitor network activity
Learn how to keep track of system and network activities in your account.

